The Cisco Annual Cyber Security Report provides a comprehensive insight into global security trends and emerging threats. The growing role of Internet of Things within industries has caught the attention of several security analysts and hit men, making it a hot topic within the 2018 Cisco report. It has been reported that 69% of respondents considered their Operational Technology equipment to be a viable attack choice, while 31% of security professionals have already experienced some type of cyber-attacks on their Operational-Technology equipment.
The Cisco Annual Cyber Security Report provides a comprehensive insight into global security trends and emerging threats. The growing role of Internet of Things within industries has caught the attention of several security analysts and hit men, making it a hot topic within the 2018 Cisco report. It has been reported that 69% of respondents considered their Operational Technology equipment to be a viable attack choice, while 31% of security professionals have already experienced some type of cyber-attacks on their Operational-Technology equipment.
So, how should an Industrial Control System be protected? How can organizations ensure stringent security techniques for their Operational Technology equipment, similar to those followed by Information Technology infrastructure?
It must be thoroughly understood that in addition to being vulnerable, Industrial Control Systems hold access to a company’s operational hardware that directly determines its productivity. While a breach in a file server can be damaging, a ransomware takeover of the industrial control system can shutdown operations, or worse lead to abnormal operational behavior that can lead to mortal danger.
Securing the Network
Firstly, industrial organizations should ensure they have a good network design, with well-defined boundaries. The ISA IEC-62443 standard serves as a practical guideline in segmenting networks. Next, all wireless applications should be secured, and remote access solutions should be deployed for carrying out maintenance and troubleshooting tasks. In conjunction with this, all network infrastructure equipment should be monitored.
Securing Endpoints
Most OT professionals are convinced that their infrastructure’s endpoints are tightly secured from digital attacks through specialized protocols, firewalls and anti-malware. However, the edge erodes quickly and leads to vulnerability when employees are allowed to bring their digital devices, e.g. Laptops, Smartphones, etc. to work and connect them with the company’s network.
To deal with this issue, companies should ensure their endpoints are secure, prohibiting staff from connecting to corporate networks. Furthermore, digital policies must be in place such as prohibition on USB connectivity, phantom Wi-Fi hotspots, etc.
A company can take the first step towards securing their endpoints by starting off with asset discovery that would help them carry out an inventory check of each endpoint. Next, they can define controls and automate these to assure the presence of protection. Finally, these endpoints can be monitored constantly, and a reaction can be elicited upon unauthorized changes.
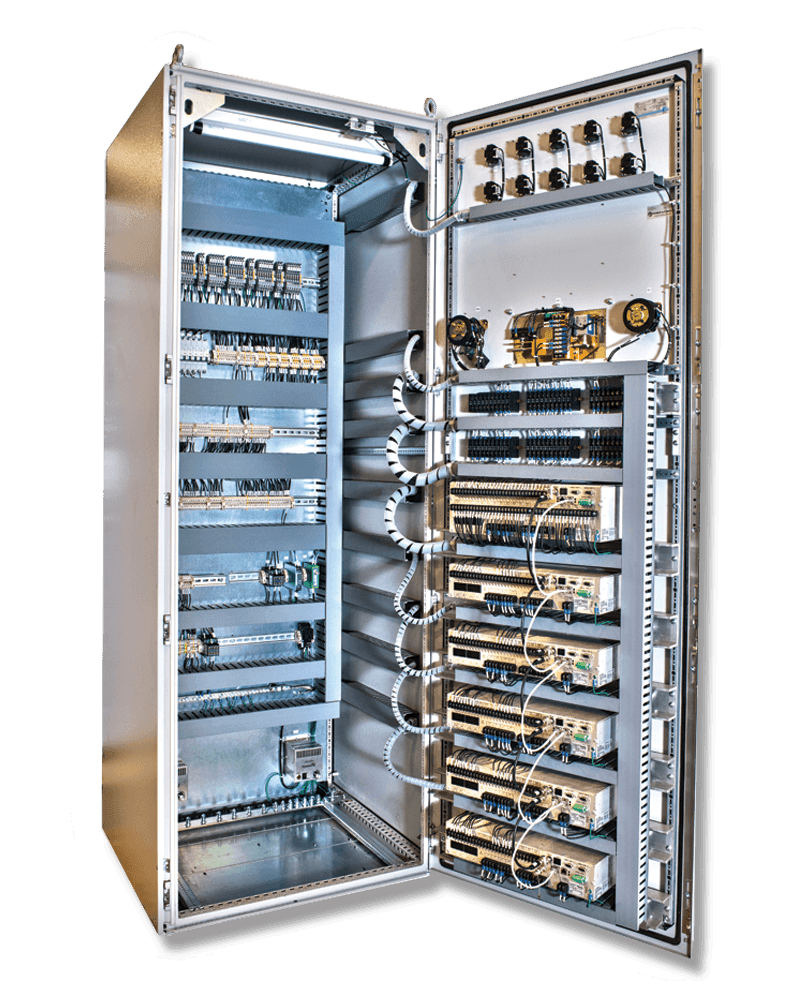
Securing Controllers
Industrial environments are composed of physical systems such as PLCs, actuators, sensors, etc. Controllers act as specialized computers to control highly diversified industrial equipment, and due to their increased sophisticated nature are prone to malware attacks.
There have been documented cases where malicious actors have gained access to PLCs, PACs or Industrial PCs, wreaking havoc within the system, even causing physical destruction. One of the most infamous cases is that of Stuxnet, when Siemens’ PLCs controlling high-speed centrifuges were targeted leading to physical damage as well as irreversible loss of productivity. Once again, even in this case, the malware made its way through the network, and if stringent network control policies are established, such episodes can be avoided.
In addition to perimeter firewalls and virtual private networks, access-control and activity logging must be implemented to ensure that only certain individuals have access to high-end systems. Furthermore, the presence of anti-malware software can help catch any dangerous piece of code that has slipped through the initial lines of defense.